When we had to scan a Typo3 instance, we searched for a scanner, similiar to WPScan for WordPress. Because we did not found one, Javan and I created such a scanner for Typo3 CMS: Typo3AccessChecker
This scanner focuses on pages in a Typo3 instance, that should not be accessible without authorization. While testing our scanner, we found out that the most of the scanned Typo3 instances were not adequately protected. It is very important to recognize missing access restrictions to avoid successful attacks through exposed logfiles , config files etc.
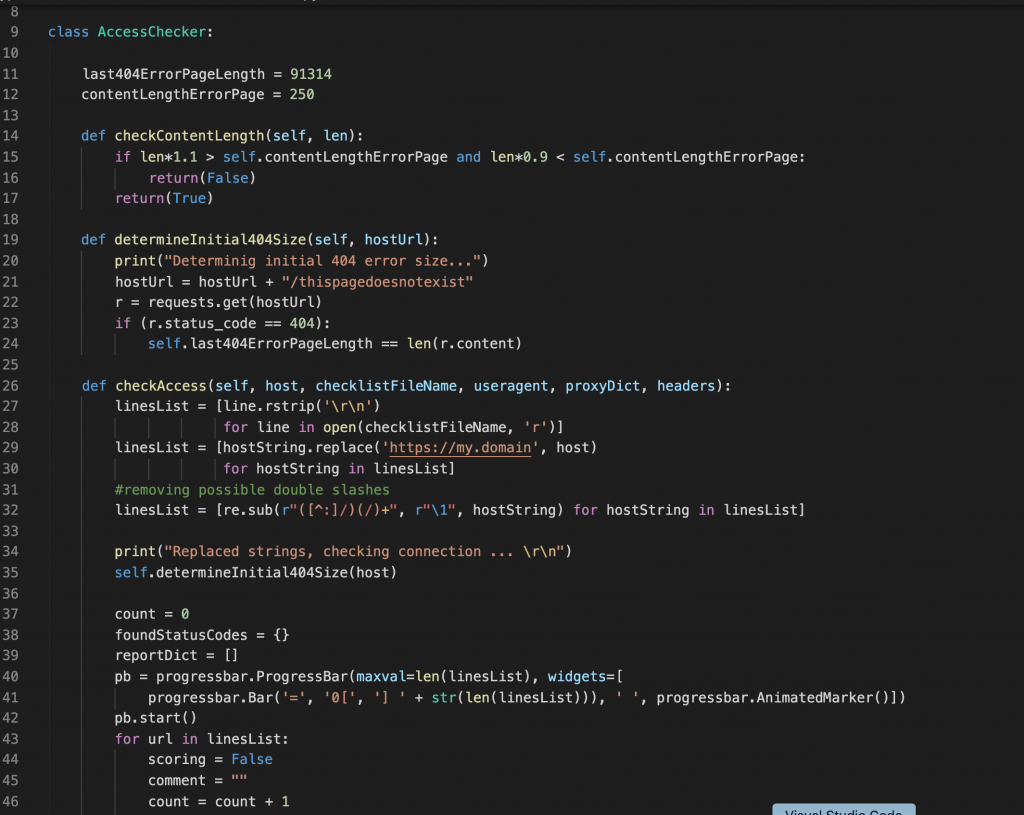
The scanner contains a default list of files that should not be accessible, but this checklist can be expanded with your own needs, in case you have plugins that have special pages that should not be accessible.
For pentesting Typo3, I can recommend the following tools and pages:
- Our Typo3AccessScanner
- The Typo3 security advisories
- Typo3Enumerator to enumerate plugins for information gathering
Feel free to open feature or merge requests on our AccessScanner or to contact me for questions 🙂